Unveiling IoT Security Vulnerabilities in IoT Enabled Devices: A Comprehensive Guide
In our increasingly connected world, the Internet of Things (IoT) has become an indispensable part of daily life and industrial operations. From smart home devices that manage our comfort to complex Industrial IoT (IIoT) systems optimizing manufacturing, these interconnected devices promise unparalleled convenience and efficiency. However, this vast network of sensors, actuators, and computing power also introduces a complex web of IoT security vulnerabilities in IoT enabled devices that demand immediate and expert attention. Understanding these inherent weaknesses is not merely an academic exercise; it's a critical step towards safeguarding personal data, operational integrity, and even physical safety from escalating cybersecurity risks. This comprehensive guide delves deep into the most prevalent vulnerabilities, their potential impact, and actionable strategies to fortify your IoT ecosystem against sophisticated threat actors.
The Ubiquitous IoT Landscape and Its Inherent Risks
The proliferation of IoT devices is staggering, with billions already deployed globally and projections pointing towards tens of billions within the next few years. This rapid expansion, while transformative, has often prioritized speed-to-market and functionality over robust security measures. Many IoT devices are designed with limited processing power, memory, and battery life, making traditional security protocols challenging to implement. Furthermore, the sheer diversity of IoT devices – ranging from simple sensors to complex robotic arms – means there's no one-size-fits-all security solution. This fragmented landscape, coupled with often lax development practices, creates fertile ground for IoT security vulnerabilities to emerge and be exploited.
The challenge is compounded by the fact that many IoT devices are deployed in environments where they are difficult to monitor, manage, or update regularly. Unlike traditional IT systems, which often reside within controlled network perimeters, IoT devices can be scattered across vast geographical areas, operate autonomously, and interact with both physical and digital realms, making them prime targets for malicious exploitation. The consequences of such exploitation can range from minor privacy infringements to large-scale data breaches, critical infrastructure disruption, and even physical harm.
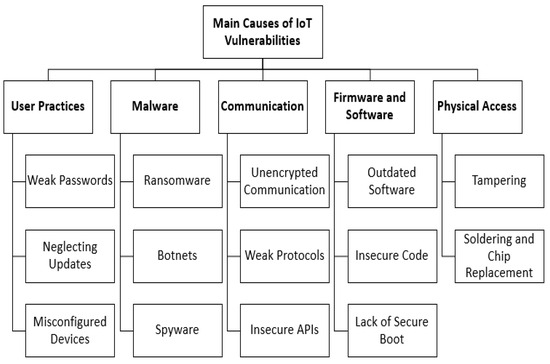
Common IoT Security Vulnerabilities: A Deep Dive
To effectively mitigate risks, it's crucial to understand the specific types of IoT security vulnerabilities that plague these devices. These weaknesses often stem from various points in the device lifecycle, from design and manufacturing to deployment and end-of-life.
Weak, Default, or Hardcoded Passwords
- Explanation: Many IoT devices ship with easily guessable default credentials (e.g., "admin/admin", "123456") or even hardcoded credentials that cannot be changed by the user. Users often fail to change these defaults, leaving devices wide open.
- Impact: Unauthorized access, device hijacking, inclusion in botnets (e.g., Mirai botnet), data exfiltration, and lateral movement within a network. This is a foundational flaw that threat actors frequently exploit first.
- Mitigation: Implement strong authentication protocols, enforce unique and complex passwords, integrate multi-factor authentication (MFA), and eliminate hardcoded credentials during the secure development lifecycle.
Insecure Network Services
- Explanation: Many IoT devices expose unnecessary network services (e.g., Telnet, FTP, unencrypted HTTP) or use outdated, vulnerable protocols. These services often lack proper authentication or encryption, making them easy targets.
- Impact: Remote code execution, denial-of-service (DoS) attacks, data interception, and unauthorized configuration changes. Poor network security is a gateway for many attacks.
- Mitigation: Disable all unnecessary services, use secure protocols (e.g., HTTPS, SSH), ensure all exposed services are patched and up-to-date, and implement strict firewall rules.
Lack of Secure Update Mechanisms
- Explanation: Many IoT devices lack robust mechanisms for over-the-air (OTA) firmware updates, or their update processes are insecure (e.g., unencrypted updates, no integrity checks). This leaves devices vulnerable to known exploits long after they've been discovered.
- Impact: Persistent vulnerabilities, difficulty in patching vulnerabilities, device compromise, and the inability to fix security flaws discovered post-deployment. Outdated device firmware is a critical risk factor.
- Mitigation: Implement secure, encrypted, and authenticated OTA update mechanisms. Ensure firmware updates are signed and verified, and provide clear instructions for users on how to update their devices.
Insufficient Data Encryption and Privacy Controls
- Explanation: Data transmitted by IoT devices (e.g., sensor readings, video feeds, personal information) is often not encrypted, or weak encryption standards are used. Furthermore, devices may collect excessive data without proper consent or clear privacy policies.
- Impact: Data breaches, privacy violations, identity theft, unauthorized surveillance, and exposure of sensitive information. This directly impacts user trust and can lead to significant regulatory fines related to privacy concerns.
- Mitigation: Implement strong, end-to-end encryption for all data in transit and at rest. Adopt a "privacy by design" approach, minimizing data collection and providing users with granular control over their data.
Insecure APIs and Cloud Interfaces
- Explanation: Many IoT devices rely on cloud services and APIs for functionality, remote control, and data storage. Insecure API design, weak authentication for cloud interfaces, or misconfigured cloud services can expose vast amounts of data.
- Impact: Unauthorized access to device data, remote control of devices, manipulation of data, and large-scale data breaches from cloud repositories.
- Mitigation: Implement robust API security measures, including strong authentication, authorization, rate limiting, and input validation. Regularly audit cloud configurations and adhere to cloud security best practices.
Physical Tampering and Supply Chain Attacks
- Explanation: For devices in accessible locations, physical tampering can bypass software security. Additionally, vulnerabilities can be introduced during the manufacturing process or supply chain (e.g., malicious components, compromised firmware loaded at the factory).
- Impact: Device compromise, intellectual property theft, introduction of backdoors, and widespread compromise if many devices from a single vendor are affected.
- Mitigation: Implement tamper detection mechanisms, secure boot processes, and rigorous supply chain vetting. Adopt a comprehensive secure development lifecycle for hardware and software.
Lack of Device Management and Decommissioning
- Explanation: Many IoT devices lack proper lifecycle management tools, making it difficult to monitor their security posture, revoke access, or securely decommission them at the end of their life.
- Impact: Orphaned devices remaining active on networks, unmonitored devices becoming attack vectors, and sensitive data remaining on retired devices.
- Mitigation: Implement robust device management platforms, clear policies for device decommissioning, and secure data erasure procedures.
The Far-Reaching Impact of IoT Security Breaches
The consequences of exploited IoT security vulnerabilities extend far beyond mere inconvenience. For consumers, a compromised smart home device could lead to privacy invasion, financial fraud, or even physical danger if locks or alarms are tampered with. Imagine a smart thermostat being hacked to cause a fire, or a security camera becoming an unauthorized surveillance tool. For businesses, especially those leveraging Industrial IoT, the impact can be catastrophic:
- Financial Losses: Direct costs from data breaches, regulatory fines, legal fees, and reputational damage.
- Operational Disruption: Downtime in critical infrastructure, manufacturing lines, or supply chains due to device manipulation or DoS attacks.
- Data Theft and Espionage: Loss of sensitive customer data, intellectual property, or competitive intelligence.
- Safety and Physical Harm: In critical applications (e.g., healthcare, automotive, industrial control systems), a security breach could lead to equipment malfunction, accidents, or even loss of life.
- Erosion of Trust: Consumers and businesses will lose faith in IoT technology if security cannot be guaranteed, hindering adoption and innovation.
Fortifying Your IoT Ecosystem: Practical Mitigation Strategies
Addressing IoT security vulnerabilities requires a multi-layered approach, involving manufacturers, developers, enterprises, and individual users. Proactive measures are always more effective than reactive responses.
Implementing Robust Authentication and Authorization
- Strong, Unique Passwords: Change all default passwords immediately upon device setup. Use long, complex, and unique passwords for each device.
- Multi-Factor Authentication (MFA): Enable MFA wherever available for IoT devices and associated cloud services.
- Least Privilege Principle: Ensure devices and users only have the minimum necessary access rights required for their function.
Ensuring Secure Device Firmware and Software Updates
Regularly check for and apply updates to device firmware and software. Manufacturers must provide secure, signed, and verifiable updates, and users must prioritize installing them. Automate updates where possible, but ensure they are authenticated and encrypted to prevent malicious injections.
Network Segmentation and Access Control
Isolate IoT devices on a separate, dedicated network segment (e.g., a VLAN) from your main corporate or home network. Implement strict firewall rules to control traffic to and from IoT devices, blocking unnecessary outbound connections and restricting inbound access to only essential services. This enhances overall network security.
Data Encryption and Privacy by Design
Demand devices that support strong encryption standards for data both in transit and at rest. For developers and manufacturers, bake security and privacy into the initial design phase (secure development lifecycle) rather than bolting it on later. Minimize data collection and provide clear consent mechanisms.
Supply Chain Security and Vendor Vetting
For enterprises, rigorously vet IoT device manufacturers and suppliers for their security practices. Understand their secure development lifecycle, patching policies, and incident response capabilities. Favor vendors with a strong security reputation and certifications.
Regular Security Audits and Penetration Testing
For complex IoT deployments, conduct regular security audits and penetration tests to identify and address IoT security vulnerabilities before threat actors can exploit them. This proactive approach helps uncover hidden cybersecurity risks.
User Awareness and Education
Educate users (both consumers and employees) about the risks associated with IoT devices and best practices for securing them. Simple steps like changing default passwords, understanding privacy settings, and recognizing phishing attempts can significantly reduce the attack surface.
The Role of Standards and Regulations in IoT Security
Governments and industry bodies are increasingly recognizing the critical need for robust IoT security. Standards like ETSI EN 303 645 (Cyber Security for Consumer IoT) and initiatives from organizations like NIST are providing frameworks for secure IoT development and deployment. These guidelines emphasize principles such as security by design, vulnerability disclosure policies, and the provision of regular security updates. Adherence to these evolving standards will be crucial for manufacturers to build trust and for users to select secure devices.
Frequently Asked Questions About IoT Security Vulnerabilities
What are the most common IoT security vulnerabilities?
The most common IoT security vulnerabilities include weak or default passwords, insecure network services, lack of secure update mechanisms for device firmware, insufficient data encryption, and insecure APIs. These weaknesses often stem from a rushed development process or a lack of focus on security during the product's secure development lifecycle, leaving devices susceptible to exploitation by threat actors.
How can I protect my smart home devices from cybersecurity risks?
To protect your smart home devices from cybersecurity risks, always change default passwords to strong, unique ones, enable multi-factor authentication, and segment your IoT devices onto a separate Wi-Fi network if possible. Regularly check for and install device firmware updates, as these often contain critical security patches. Be mindful of the data your devices collect and ensure privacy concerns are addressed by checking privacy settings and policies.
What role does device firmware play in IoT security?
Device firmware is the embedded software that controls an IoT device's basic functions. It plays a crucial role in IoT security because vulnerabilities within the firmware can grant attackers deep control over the device, even enabling remote code execution or unauthorized access. Ensuring secure, authenticated, and regularly updated firmware is paramount for preventing compromise and for effective patching vulnerabilities.
Why is network security crucial for IoT deployments?
Network security is crucial for IoT deployments because it acts as the first line of defense against external threats. By segmenting IoT devices, implementing firewalls, and monitoring network traffic, you can prevent unauthorized access to devices, contain potential breaches, and limit the impact of compromised devices on your broader network. Without robust network security, even a single vulnerable IoT device can become a gateway for widespread attacks, leading to significant data breaches or operational disruption.
What are the risks of unpatched IoT devices?
The risks of unpatched IoT devices are substantial. An unpatched device remains vulnerable to known exploits that have already been publicly disclosed, making it an easy target for threat actors. These risks include being hijacked for botnets, data theft, remote control by malicious actors, and serving as an entry point for lateral movement into a broader network. Regular patching vulnerabilities is essential to maintain the security posture of your IoT ecosystem and mitigate ongoing cybersecurity risks.

0 Komentar