Complete Guide
In our increasingly interconnected world, the Internet of Things (IoT) has become an indispensable part of daily life, from smart homes and wearables to industrial automation and critical infrastructure. Yet, with this pervasive connectivity comes an unprecedented volume of sensitive data, making IoT data encryption methods not just a best practice, but an absolute necessity. As a professional SEO expert and content strategist, I understand the critical importance of safeguarding this digital frontier. This comprehensive guide delves deep into the various encryption techniques and strategies essential for protecting sensitive data flowing through IoT ecosystems, ensuring robust data security and maintaining user trust in an era of escalating cyber threats.
The Imperative of IoT Data Encryption: Why It Matters More Than Ever
The sheer scale and diversity of IoT devices mean that data is generated, transmitted, and stored at every conceivable point. This data often includes highly sensitive information: personal health records from wearables, financial transactions from smart payment systems, proprietary industrial processes from factory sensors, and even real-time location data. The potential for misuse, unauthorized access, or outright breach of this data presents significant risks, ranging from financial fraud and privacy violations to operational disruptions and even physical harm.
Without robust IoT data security measures, particularly strong encryption, these vulnerabilities become glaring entry points for malicious actors. Consider the implications of a compromised smart home system revealing occupancy patterns, or an industrial IoT sensor network being manipulated to disrupt critical operations. Beyond the immediate impact, organizations face severe reputational damage, loss of customer trust, and hefty fines under stringent data protection regulations like GDPR, CCPA, and HIPAA. Therefore, understanding and implementing effective IoT data encryption methods is foundational to building resilient and trustworthy IoT deployments.
Understanding the IoT Attack Surface and Encryption's Role
To effectively protect sensitive data, one must first comprehend the multifaceted attack surface of an IoT ecosystem. Unlike traditional IT networks, IoT introduces unique challenges due to the sheer number of devices, their varied capabilities, and often remote or unattended deployments. The attack surface typically spans three primary layers:
- Device Level: Individual IoT devices themselves, which can be resource-constrained and vulnerable to physical tampering, firmware exploits, or insecure default credentials.
- Network Level: The communication channels through which devices transmit data, including Wi-Fi, cellular, LoRaWAN, Zigbee, and Bluetooth. Interception of data in transit is a major concern here.
- Cloud/Backend Level: The servers, databases, and cloud platforms that collect, process, and store aggregated IoT data. These are often targets for large-scale data breaches.
Effective IoT data encryption methods must address all these layers, aiming for true end-to-end encryption. This means data is encrypted at the point of origin (the device), remains encrypted while in transit across networks, and is only decrypted at its final, secure destination (e.g., a trusted cloud server or application), or is processed in an encrypted state. This holistic approach minimizes exposure at every stage of the data lifecycle.
Core IoT Data Encryption Methods and Protocols
Securing IoT data requires a multi-pronged approach, leveraging different encryption techniques depending on the data's state: at rest, in transit, or in use.
Encryption at Rest (Data Storage)
Data stored on IoT devices, gateways, or backend servers must be encrypted to prevent unauthorized access if the storage medium is compromised. This is crucial for data privacy.
- Full Disk Encryption (FDE): For IoT gateways or more sophisticated edge devices with significant storage, FDE encrypts the entire storage drive. This ensures that if the device is stolen or physically accessed, the data remains unreadable without the correct decryption key.
- Database Encryption: Backend servers often store vast amounts of collected IoT data in databases. Database encryption protects this data by encrypting individual fields, columns, or the entire database, often with transparent data encryption (TDE) features provided by database management systems.
- File-Level Encryption: For specific files or folders on a device or server, file-level encryption can be applied. This offers granular control over which data is protected.
The effectiveness of encryption at rest heavily relies on robust key management, ensuring that encryption keys are securely generated, stored, and accessed only by authorized entities.
Encryption in Transit (Data Communication)
Protecting data as it moves between devices, gateways, and cloud platforms is paramount. This is where secure communication protocols come into play.
- TLS/SSL (Transport Layer Security/Secure Sockets Layer): The gold standard for securing internet communication, TLS (the successor to SSL) is widely used to encrypt data between IoT devices and cloud servers over TCP/IP networks (e.g., HTTPS). It provides confidentiality, integrity, and server authentication. For resource-constrained devices, lightweight TLS implementations are often employed.
- DTLS (Datagram Transport Layer Security): A variant of TLS designed for UDP-based protocols, DTLS is essential for securing communication in environments where UDP is preferred for its low overhead, such as with CoAP (Constrained Application Protocol) in constrained IoT networks.
- IPsec (Internet Protocol Security): Operating at the network layer, IPsec provides strong security for IP communications, including authentication and encryption. It's often used in industrial IoT (IIoT) and enterprise settings for secure VPNs and communication between gateways or edge devices.
- Secure IoT Protocols (e.g., MQTT over TLS, CoAP over DTLS): Many IoT applications rely on specific messaging protocols like MQTT or CoAP. To secure these, they are typically layered over TLS or DTLS, leveraging the underlying transport security mechanisms. For instance, MQTT security is often achieved by running MQTT over TLS.
Implementing mutual authentication (where both the client device and the server verify each other's identity) alongside these protocols significantly enhances security, preventing unauthorized devices from connecting to the network or legitimate devices from connecting to rogue servers.
Encryption in Use (Homomorphic Encryption, Secure Enclaves)
This is an emerging and highly specialized area, focusing on protecting data while it is being processed. It addresses the vulnerability of data in memory or during computation.
- Homomorphic Encryption (HE): A groundbreaking, albeit computationally intensive, encryption algorithm that allows computations to be performed on encrypted data without decrypting it first. The result of the computation remains encrypted and, when decrypted, matches the result as if the operations were performed on unencrypted data. While still largely a research topic for broad IoT application, it holds immense promise for privacy-preserving analytics in sensitive domains like healthcare.
- Secure Enclaves/Trusted Execution Environments (TEEs): Hardware-based isolation mechanisms (e.g., ARM TrustZone, Intel SGX) that create a secure, isolated environment within a processor. Sensitive data and code can be processed within this enclave, protected from the rest of the system, even if the operating system or other applications are compromised. This is crucial for protecting cryptographic keys and sensitive computations on the device itself.
Cryptographic Algorithms for IoT Security
The choice of encryption algorithms is fundamental to the strength and efficiency of any IoT security solution. Different algorithms are suited for different purposes and device capabilities.
Symmetric Key Algorithms
Symmetric encryption uses a single, shared key for both encryption and decryption. They are generally faster and require less computational power, making them ideal for resource-constrained IoT devices.
- AES (Advanced Encryption Standard): The most widely adopted symmetric block cipher. AES is highly efficient and secure, available in 128-bit, 192-bit, and 256-bit key lengths. It's excellent for bulk data encryption on devices and in transit once a secure key exchange has occurred.
- ChaCha20-Poly1305: A modern stream cipher that offers high performance, especially on processors without dedicated AES hardware acceleration. It's often paired with the Poly1305 message authentication code for authenticated encryption, providing both confidentiality and integrity. Its lightweight nature makes it suitable for very constrained IoT environments.
Asymmetric Key Algorithms
Asymmetric (or public-key) encryption uses a pair of mathematically linked keys: a public key for encryption and a private key for decryption. They are slower than symmetric algorithms but are crucial for secure key exchange, digital signatures, and device authentication.
- RSA (Rivest–Shamir–Adleman): Historically popular for digital signatures and key exchange. While still secure with sufficiently long keys, its computational overhead can be a concern for very low-power IoT devices.
- ECC (Elliptic Curve Cryptography): Offers equivalent security to RSA with significantly smaller key sizes, leading to faster computations and lower power consumption. This makes ECC a prime candidate for lightweight cryptography in resource-constrained IoT devices for key exchange (e.g., ECDH - Elliptic Curve Diffie-Hellman) and digital signatures (e.g., ECDSA - Elliptic Curve Digital Signature Algorithm).
Hashing Algorithms
While not encryption, hashing algorithms are critical components of cryptographic protocols for IoT data integrity and authentication. They produce a fixed-size output (hash) from input data, making it computationally infeasible to reverse the process or find two inputs that produce the same hash.
- SHA-256, SHA-3: Secure Hash Algorithm variants used for verifying data integrity (ensuring data hasn't been tampered with), creating digital signatures for firmware updates, and securely storing passwords. They are vital for establishing trust in the data received from IoT devices.
The Critical Role of Key Management in IoT Encryption
Even the strongest IoT data encryption methods are only as secure as their keys. Key management is arguably the most challenging aspect of IoT security due to the sheer number of devices, their geographic distribution, and their often limited processing capabilities. Poor key management is a leading cause of security vulnerabilities.
Secure Key Generation and Storage
Keys must be generated securely and stored in tamper-resistant environments. This prevents keys from being extracted or compromised.
- Hardware Security Modules (HSMs): Dedicated cryptographic processors that generate, store, and manage cryptographic keys within a secure physical boundary. They are the gold standard for high-security environments, often used in cloud backends and gateways.
- Trusted Platform Modules (TPMs): Secure cryptoprocessors embedded in many computing devices, offering secure key storage and cryptographic operations. They are increasingly found in more capable IoT devices and gateways.
- Secure Elements (SEs): Small, tamper-resistant microcontrollers designed to securely store cryptographic keys and perform operations in highly constrained environments, like smart cards or embedded within IoT microcontrollers.
Key Distribution and Rotation
Distributing keys securely to billions of devices and rotating them periodically to limit the impact of potential compromises are complex tasks.
- Over-the-Air (OTA) Updates: Secure OTA update mechanisms are crucial for delivering new keys and rotating existing ones, often leveraging asymmetric cryptography for authenticity and integrity.
- Device Provisioning: Initial key injection during manufacturing or secure field provisioning processes are vital to establish the root of trust.
- Key Rotation Policies: Implementing policies to regularly change keys mitigates the risk associated with long-lived keys.
Lifecycle Management
Effective key management encompasses the entire lifecycle of a key, from generation to destruction.
- Provisioning: Securely injecting initial keys into devices.
- Usage: Ensuring keys are used only for their intended purpose and within defined security boundaries.
- Rotation: Periodically changing keys to enhance security.
- Revocation: Disabling compromised or retired keys.
- Destruction: Securely erasing keys when they are no longer needed.
For more insights, consider exploring best practices in IoT device provisioning.
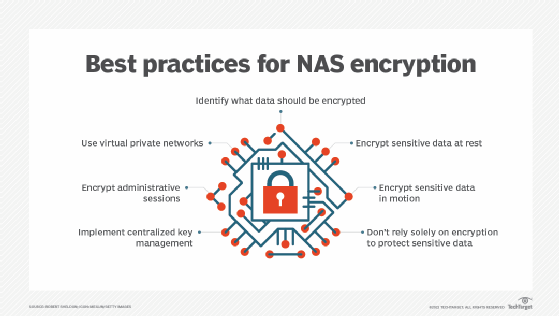
Best Practices for Implementing Robust IoT Data Encryption
Implementing effective IoT data encryption methods goes beyond merely selecting algorithms; it requires a holistic security strategy.
- Adopt a Holistic Security Approach (Defense in Depth): Encryption is one layer of a comprehensive defense in depth strategy. Combine it with physical security, network segmentation, secure coding practices, access control, and continuous monitoring. No single solution is a silver bullet.
- Prioritize Device-Level Security: Ensure secure boot mechanisms prevent unauthorized firmware, implement tamper detection, and enable secure storage for cryptographic keys and sensitive data directly on the device. Regular and secure firmware updates are non-negotiable for patching vulnerabilities.
- Implement Network Segmentation: Isolate IoT devices from critical enterprise networks. This limits the lateral movement of attackers even if an IoT device is compromised, reducing the blast radius of a potential breach.
- Regular Security Audits and Penetration Testing: Proactively identify vulnerabilities in your IoT ecosystem. This includes reviewing code, configurations, and network architectures. Leverage threat intelligence to stay ahead of emerging threats.
- Comply with Standards and Regulations: Adhere to relevant industry standards (e.g., ISO 27001, NIST cybersecurity framework) and data protection regulations (GDPR, CCPA, HIPAA, NIS2). These frameworks provide guidelines for robust security practices, including data encryption.
- Educate Stakeholders: Ensure that developers, operators, and end-users understand the importance of data privacy and their role in maintaining security. Human error remains a significant vulnerability.
- Plan for Scalability: As your IoT deployment grows, your encryption and key management solutions must scale seamlessly without compromising performance or security.
Actionable Tip: Start with a thorough risk assessment of your specific IoT deployment to identify the most sensitive data and critical points of vulnerability. This will inform your choice and implementation of encryption methods.
Challenges and Future Trends in IoT Encryption
While significant progress has been made, several challenges persist in IoT encryption:
- Resource Constraints: Many IoT devices have extremely limited processing power, memory, and battery life, making it challenging to implement complex cryptographic operations without impacting performance or device longevity. This drives the need for highly optimized, lightweight cryptography.
- Scalability: Managing encryption keys and secure updates for billions of diverse devices across vast geographical areas presents immense logistical and technical hurdles.
- Legacy Devices: Integrating older, non-secure IoT devices into modern encrypted ecosystems can be difficult and costly, often requiring secure gateways to act as intermediaries.
Looking ahead, future trends in IoT encryption include:
- Post-Quantum Cryptography (PQC): Research into PQC algorithms is accelerating to prepare for the advent of quantum computers, which could potentially break current asymmetric encryption schemes. IoT will need to adopt these new algorithms for long-term security.
- Hardware-Accelerated Cryptography: More IoT chipsets are integrating dedicated hardware modules for cryptographic operations, improving performance and efficiency for encryption and decryption.
- AI/ML for Anomaly Detection: While not encryption itself, AI and machine learning are increasingly used to detect anomalous behavior in encrypted IoT traffic, signaling potential breaches or attacks that bypass traditional security measures.
Frequently Asked Questions
What is the primary purpose of IoT data encryption?
The primary purpose of IoT data encryption methods is to protect sensitive data from unauthorized access, modification, or disclosure throughout its lifecycle – whether it's stored on a device, in transit across a network, or being processed. It ensures confidentiality and integrity, safeguarding user privacy and operational security against cyber threats.
How does TLS/SSL protect IoT data in transit?
TLS/SSL protects IoT data in transit by creating a secure, encrypted channel between an IoT device and a server. It uses a combination of symmetric and asymmetric encryption algorithms to achieve three main goals: 1) Confidentiality: Encrypting the data payload so only the intended recipient can read it. 2) Integrity: Ensuring the data hasn't been tampered with during transmission using cryptographic hashes. 3) Authentication: Verifying the identity of the server (and optionally the client device through device authentication) to prevent man-in-the-middle attacks, thus enabling secure communication.
Why is key management so critical for IoT encryption?
Key management is critical because the strength of any encryption relies entirely on the security of its keys. If encryption keys are compromised, stolen, or poorly managed, even the strongest IoT data encryption methods become ineffective. For IoT, the challenge is amplified by the vast number of devices, their physical distribution, and resource constraints, necessitating robust processes for secure key generation, storage, distribution, rotation, and revocation throughout the entire key lifecycle to maintain data security.
What are the main challenges when encrypting data on resource-constrained IoT devices?
The main challenges for encrypting data on resource-constrained IoT devices include limited processing power, which can make complex encryption algorithms slow and drain battery life; scarce memory for storing keys and cryptographic libraries; and the difficulty of implementing secure hardware elements for key management. This often necessitates the use of lightweight cryptography and careful optimization of encryption protocols to balance security

0 Komentar