Safeguard Your Enterprise: Download Your Free Cybersecurity Incident Response Plan Template Today
In today's digital landscape, a cybersecurity incident response plan template free is not just a luxury; it's a critical necessity for any organization aiming to protect its digital assets and maintain business continuity. As cyber threats grow in sophistication and frequency, having a robust, actionable plan in place can mean the difference between a minor disruption and a catastrophic data breach. This comprehensive guide will walk you through the essential components of an effective incident response framework, highlight what to look for in a free template, and provide practical steps to customize it for your unique operational needs. Discover how a well-structured plan empowers your team to react swiftly, mitigate damage, and recover efficiently from any cyber attack, ensuring your organization is prepared for the inevitable.
Why a Cybersecurity Incident Response Plan is Non-Negotiable in Today's Threat Landscape
The question is no longer if your organization will face a cyber incident, but when. From ransomware attacks to sophisticated phishing campaigns and insider threats, the potential vectors for disruption are numerous and constantly evolving. Without a predefined incident response plan, businesses often react chaotically, leading to increased downtime, greater financial losses, reputational damage, and potential legal repercussions. A proactive approach, underpinned by a clear plan, ensures an organized, efficient, and effective response.
Studies consistently show that organizations with mature incident response capabilities experience significantly lower costs and faster recovery times following a cyber attack. This isn't just about technical fixes; it's about a holistic strategy that involves people, processes, and technology. A well-crafted plan acts as your organization's blueprint for navigating the storm, guiding every step from initial detection to full recovery and post-incident analysis. It minimizes panic, clarifies roles, and ensures a coordinated effort across all relevant departments, from IT and legal to public relations and executive leadership. Think of it as your digital fire drill, ensuring everyone knows their role when the alarm sounds.
The High Stakes of Unpreparedness
- Financial Losses: Data breaches can cost millions in recovery, fines, and lost revenue.
- Reputational Damage: Loss of customer trust and public perception can be long-lasting.
- Regulatory Fines: Non-compliance with data protection regulations (e.g., GDPR, CCPA) can result in hefty penalties.
- Operational Disruption: Extended downtime can cripple business operations and supply chains.
- Legal Liabilities: Potential lawsuits from affected parties or regulatory bodies.
Key Phases of an Effective Incident Response Plan
A robust cybersecurity incident response plan template free typically structures the response process into distinct, actionable phases, often aligned with frameworks like NIST (National Institute of Standards and Technology). Understanding these phases is crucial for building an effective and comprehensive strategy.
1. Preparation
This foundational phase occurs before any incident. It involves building the necessary infrastructure, policies, and training to handle future events. Without solid preparation, subsequent phases will be reactive and less effective.
- Policy Development: Establish clear incident response policies and procedures.
- Team Formation: Designate an incident response team (IRT) with clearly defined roles and responsibilities.
- Tooling & Technology: Implement security information and event management (SIEM) systems, intrusion detection/prevention systems (IDPS), endpoint detection and response (EDR), and forensic tools.
- Training & Drills: Conduct regular training sessions and tabletop exercises to test the plan and identify gaps.
- Communication Protocols: Define internal and external communication strategies.
2. Detection & Analysis
This phase focuses on identifying potential security incidents and thoroughly analyzing their nature, scope, and impact.
- Monitoring & Alerting: Continuously monitor networks, systems, and applications for suspicious activity.
- Triage & Prioritization: Quickly assess alerts to determine if an actual incident has occurred and prioritize based on severity and potential impact.
- Information Gathering: Collect all relevant data (logs, network traffic, system artifacts) to understand the incident's characteristics.
- Scope Definition: Determine what systems, data, and users are affected.
3. Containment
Once an incident is confirmed and analyzed, the primary goal of containment is to stop the spread of the attack and prevent further damage.
- Short-Term Containment: Isolate affected systems, disconnect from the network, or block malicious IP addresses.
- System Backups: Ensure clean backups are available for recovery.
- Long-Term Containment: Implement temporary fixes or workarounds to restore critical services while a permanent solution is developed.
4. Eradication
This phase involves removing the root cause of the incident and eliminating all traces of the attacker from the environment.
- Malware Removal: Delete malicious files, scripts, or configurations.
- Vulnerability Patching: Address the specific vulnerabilities exploited by the attacker.
- System Hardening: Implement additional security controls to prevent recurrence.
- Password Resets: Force password changes for affected accounts.
5. Recovery
The recovery phase focuses on restoring affected systems and data to normal operations, ensuring business continuity.
- System Restoration: Rebuild or restore systems from clean backups.
- Testing: Thoroughly test all restored systems and applications to ensure full functionality and security.
- Monitoring: Implement enhanced monitoring to detect any lingering threats or new vulnerabilities.
- Validation: Obtain confirmation from business owners that operations are fully restored.
6. Post-Incident Activity (Lessons Learned)
This critical phase involves a thorough review of the incident and the response, identifying areas for improvement.
- Post-Mortem Analysis: Document the incident timeline, actions taken, and outcomes.
- Lessons Learned Meeting: Conduct a formal meeting with all stakeholders to discuss what went well, what didn't, and what could be improved.
- Action Item Development: Create an action plan to address identified weaknesses in policies, procedures, or technology.
- Reporting: Generate a final report for management and relevant authorities.
What to Look For in a Free Cybersecurity Incident Response Plan Template
Finding a reliable cybersecurity incident response plan template free can significantly kickstart your planning process. However, not all templates are created equal. Here’s what to prioritize when selecting one:
- Comprehensive Coverage: The template should ideally cover all six phases of incident response (Preparation to Post-Incident Activity).
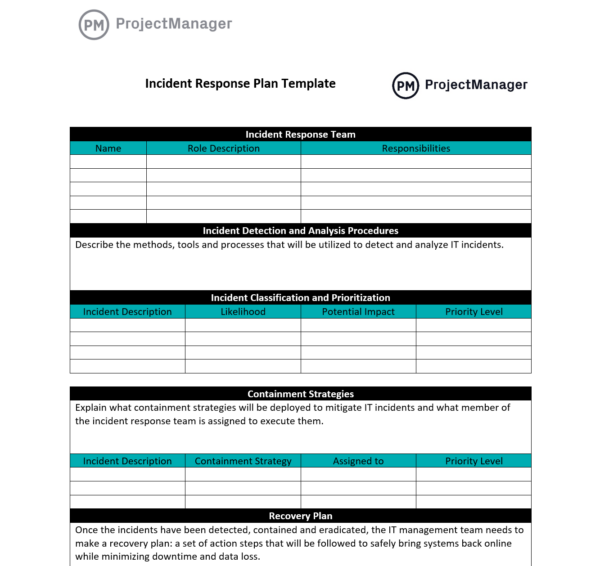
- Clear Roles and Responsibilities: It should provide sections to clearly define who is responsible for what action during an incident.
- Communication Plan: Look for templates that include sections for internal and external communication strategies, including media relations.
- Legal and Regulatory Considerations: While a template won't provide specific legal advice, it should prompt you to consider reporting requirements and data privacy regulations relevant to your industry and region.
- Checklists and Workflows: Practical checklists for each phase (e.g., a "detection checklist" or "containment checklist") are invaluable.
- Documentation Sections: Ample space or prompts for documenting incident details, actions taken, and lessons learned.
- Scalability: The template should be adaptable to the size and complexity of your organization.
- User-Friendly Format: A template that is easy to understand, navigate, and modify (e.g., in Word or Google Docs format) is preferable.
- Source Credibility: Prioritize templates from reputable cybersecurity organizations, government agencies (like NIST or CISA), or well-known security vendors.
Many organizations offer free templates as a community service or as a lead magnet. While these can be excellent starting points, remember that they are generic by nature and require significant customization.
Customizing Your Free Incident Response Template for Optimal Protection
A cybersecurity incident response plan template free is merely a framework. Its true value emerges only when meticulously customized to your organization's specific environment, risks, and resources. This customization is where the real work begins, transforming a generic document into a powerful operational tool.
Consider your unique technological stack, the types of data you handle, your regulatory obligations, and your organizational structure. For example, a healthcare provider will have different compliance requirements (like HIPAA) than a financial institution (like PCI DSS). Your customization process should be iterative and involve cross-functional teams.
Practical Steps for Tailoring Your Template:
- Identify Your Critical Assets: Map out your most valuable data, systems, and applications. What absolutely must be protected or recovered first? This informs your prioritization during an incident.
- Define Your Incident Types: Categorize the types of incidents your organization is most likely to face (e.g., phishing, ransomware, insider threat, DDoS). Tailor response procedures for each.
- Establish Your Incident Response Team (IRT): Beyond just IT, your IRT should include representatives from legal, HR, communications, and executive leadership. Clearly define roles, responsibilities, and contact information for each member.
- Develop Communication Trees: Create detailed internal and external communication plans. Who needs to be notified, by what method, and when? Include templates for internal alerts, customer notifications, and media statements.
- Integrate with Existing Plans: Ensure your incident response plan aligns with your broader <a href="[internal-link-to-business-continuity-planning]">business continuity</a> and disaster recovery plans.
- Define Escalation Paths: Clearly outline when and how incidents should be escalated to higher management or external experts.
- Document Tools and Resources: List all security tools, software, and external resources (e.g., forensic firms, legal counsel) available to your IRT.
- Set Up Reporting Procedures: Determine how incidents will be reported internally and externally (e.g., to regulators, law enforcement).
- Regularly Review and Update: Cyber threats evolve constantly. Your plan must be a living document, reviewed and updated at least annually, or after any significant organizational or technological change.
Implementing and Maintaining Your Incident Response Plan
Having a perfectly crafted cybersecurity incident response plan template free on paper is only half the battle. Effective implementation and continuous maintenance are paramount to its success. A plan that isn't practiced or updated is as good as no plan at all.
Crucial Implementation and Maintenance Activities:
- Training and Awareness: All employees, especially those on the IRT, must be trained on their roles and the procedures outlined in the plan. Regular security awareness training for the entire workforce helps reduce the likelihood of human-error-induced incidents.
- Tabletop Exercises: Conduct regular tabletop exercises where the IRT simulates responding to various cyber scenarios. These drills expose weaknesses in the plan, clarify roles, and improve team coordination under pressure.
- Live Drills/Simulations: For more mature organizations, consider conducting live simulations where actual systems are used to practice containment and recovery, within a controlled environment.
- Technology Integration: Ensure your security tools (SIEM, EDR, firewalls) are properly configured to support the detection and analysis phases of your plan. Automate alerts and data collection where possible.
- Vendor Management: If you rely on third-party vendors for services or data processing, ensure their security practices align with your incident response requirements.
- Performance Metrics: Define key performance indicators (KPIs) for your incident response program, such as mean time to detect (MTTD), mean time to contain (MTTC), and mean time to recover (MTTR). Track these metrics to gauge effectiveness.
- Continuous Improvement: Use insights gained from post-incident reviews and drills to continuously refine and improve your plan. This iterative process ensures your response capabilities mature over time.
- Budget Allocation: Ensure adequate resources are allocated for ongoing training, tool maintenance, and potential external services (e.g., incident response retainers).
By diligently implementing and maintaining your customized incident response plan, you transform a theoretical document into a practical, resilient defense mechanism. This proactive stance not only protects your organization but also demonstrates due diligence to customers, partners, and regulators, fostering trust and confidence.
Frequently Asked Questions
What is a cybersecurity incident response plan template free, and why do I need one?
A cybersecurity incident response plan template free is a pre-designed document that provides a structured framework for organizations to prepare for, detect, respond to, and recover from cyber attacks or security breaches. You need one because it provides a clear, step-by-step guide for your team, minimizing chaos, reducing damage, ensuring compliance, and accelerating recovery time during a crisis. It's an essential component of <a href="[internal-link-to-risk-management-strategy]">risk management</a> and business continuity.
How often should I update my incident response plan after using a free template?
Your incident response plan should be a living document, not a static one. It's recommended to review and update it at least annually, or whenever there are significant changes to your organization's IT infrastructure, critical assets, business operations, regulatory requirements, or the evolving threat landscape. After any actual incident or a major drill, a "lessons learned" session should lead to immediate updates.
Can a free template fully protect my organization from all cyber threats?
While a free cybersecurity incident response plan template is an excellent starting point and provides foundational structure, it cannot fully protect your organization on its own. It's a guide, not a magic shield. Full protection requires diligent customization of the template, ongoing employee training, regular drills, investment in appropriate security technologies, continuous threat intelligence monitoring, and adherence to best practices. A template is a tool; its effectiveness depends on how well you implement and maintain the complete incident response program.
What's the difference between an incident response plan and a disaster recovery plan?
A cybersecurity incident response plan focuses specifically on responding to and recovering from security incidents like data breaches, malware infections, or unauthorized access. It details the steps to identify, contain, eradicate, and recover from cyber threats. A <a href="[internal-link-to-disaster-recovery-planning]">disaster recovery plan (DRP)</a>, on the other hand, is broader and deals with recovering IT infrastructure and operations after any major disruptive event, whether it's a cyber attack, natural disaster, power outage, or hardware failure. While there's overlap (e.g., data recovery), the incident response plan is specialized for security events.

0 Komentar