Quantum Computing and Quantum Key Distribution Explained: Securing Data in the Quantum Era
The dawn of quantum computing heralds an unprecedented revolution, promising to solve problems currently intractable for even the most powerful classical supercomputers. However, this transformative power also casts a long shadow over our existing digital security infrastructure. Traditional cryptographic methods, the bedrock of modern cybersecurity, are vulnerable to the immense computational capabilities of future fault-tolerant quantum machines. This looming threat necessitates a fundamental rethink of how we protect sensitive information. Enter Quantum Key Distribution (QKD), a groundbreaking technology that leverages the very principles of quantum mechanics to establish unconditionally secure cryptographic keys, offering a robust defense against even the most sophisticated quantum attacks. This comprehensive guide will explain the intricacies of QKD, its crucial role in quantum-safe communication, and why it's becoming an indispensable component of future cybersecurity strategies.
Understanding the Quantum Threat to Classical Encryption
For decades, our digital world has relied on the mathematical complexity of certain problems to ensure data security. Public-key cryptography, foundational to secure online transactions, relies on algorithms like RSA and ECC. These algorithms derive their strength from the difficulty of factoring large numbers or solving elliptic curve discrete logarithm problems. While classical computers would take billions of years to break these codes, quantum algorithms threaten to dismantle them with alarming speed.
Shor's Algorithm: The Cryptographic Game Changer
- Exponential Speedup: Developed by Peter Shor, Shor's algorithm can efficiently factor large numbers and solve discrete logarithm problems, effectively rendering RSA and ECC vulnerable. This isn't just a minor improvement; it's an exponential speedup that would allow a sufficiently powerful quantum computer to decrypt most of the encrypted data we currently send and store.
- Grover's Algorithm: While not directly breaking public-key cryptography, Grover's algorithm offers a quadratic speedup for searching unsorted databases. This could significantly reduce the effective key length of symmetric encryption algorithms like AES, making brute-force attacks more feasible.
- The "Harvest Now, Decrypt Later" Threat: Malicious actors are already collecting encrypted data, anticipating the arrival of quantum computers capable of decrypting it later. This emphasizes the urgency of transitioning to quantum-resistant encryption methods.
The potential for a "quantum apocalypse" for current encryption methods underscores the critical need for solutions like quantum key distribution to safeguard sensitive information well into the future. [Learn more about the basics of quantum computing here]
What is Quantum Key Distribution (QKD)?
Unlike classical encryption, which relies on mathematical hardness, Quantum Key Distribution (QKD) leverages the fundamental laws of quantum mechanics to guarantee the security of a shared secret key between two parties. It's crucial to understand that QKD is not a method for encrypting data itself; rather, it's a protocol for securely exchanging the encryption key that will then be used by classical cryptographic algorithms (like AES) to encrypt and decrypt the actual data. This key exchange mechanism is what makes QKD revolutionary.
The Core Principle: Unconditional Security from Physics
The security of QKD doesn't depend on the computational limitations of an adversary or unproven mathematical assumptions. Instead, it relies on immutable laws of physics:
- No-Cloning Theorem: It's impossible to create an identical copy of an unknown quantum state. This means an eavesdropper cannot simply copy the quantum information without disturbing it.
- Measurement Disturbance: Any attempt to measure or observe a quantum system inevitably alters its state. This fundamental principle is the cornerstone of QKD's security. If an eavesdropper (often called "Eve") tries to intercept the quantum key exchange, her mere act of observation will introduce detectable errors, immediately alerting the legitimate parties (Alice and Bob) to her presence.
This unique property means that security is guaranteed by the laws of physics, not by computational complexity, offering a level of assurance that classical cryptography cannot match against a quantum adversary.
The Science Behind QKD: Quantum Principles in Action
To fully grasp how QKD achieves its unparalleled security, it's essential to understand the quantum phenomena it exploits:
Superposition, Entanglement, and the No-Cloning Theorem
- Superposition: A quantum bit, or qubit, can exist in a superposition of multiple states simultaneously (e.g., both 0 and 1 at the same time), unlike a classical bit which must be either 0 or 1. This allows for rich information encoding.
- Quantum Entanglement: Two or more qubits can become "entangled," meaning their fates are linked, regardless of distance. Measuring the state of one entangled qubit instantaneously influences the state of the other, even if they are light-years apart. This phenomenon forms the basis of some advanced QKD protocols (like E91).
- No-Cloning Theorem: As mentioned, this fundamental theorem of quantum mechanics states that an arbitrary unknown quantum state cannot be perfectly copied. This is vital for QKD, as it prevents an eavesdropper from making a perfect copy of the quantum key and then retransmitting it to avoid detection. Any attempt to copy will inevitably disturb the original state, making the eavesdropper's presence known.
Photon Polarization as Information Carrier
In most practical QKD implementations, information is encoded in the polarization states of single photons. Photons, being light particles, can have their polarization oriented in various ways. For instance, they can be vertically, horizontally, diagonally, or anti-diagonally polarized. These different polarization states can represent the 0s and 1s of the cryptographic key. The genius of QKD lies in how these states are transmitted and measured.
How QKD Protocols Work: A Deep Dive into BB84
The most widely known and implemented QKD protocol is BB84, developed by Charles Bennett and Gilles Brassard in 1984. It beautifully illustrates the principles of quantum mechanics in action for secure key exchange.
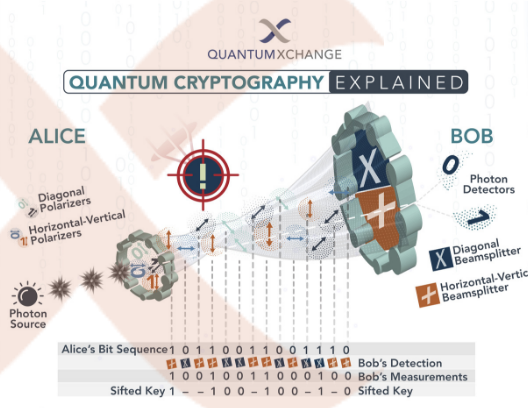
The BB84 Protocol Explained (Simplified)
Imagine Alice (the sender) wants to send a secret key to Bob (the receiver), and Eve (the eavesdropper) is trying to listen in.
- Photon Transmission (Alice to Bob):
- Alice generates a random sequence of bits (0s and 1s) for her key.
- For each bit, she randomly chooses one of two measurement bases to encode it:
- Rectilinear Basis: Vertical (|) or Horizontal (-) polarization.
- Diagonal Basis: Diagonal (/) or Anti-diagonal () polarization.
- For example, a '0' could be encoded as vertical polarization in the rectilinear basis, or anti-diagonal in the diagonal basis. A '1' would be horizontal in rectilinear, or diagonal in diagonal.
- Alice sends each photon, one by one, to Bob.
- Photon Reception and Measurement (Bob):
- For each incoming photon, Bob randomly chooses one of the two measurement bases (rectilinear or diagonal) to measure its polarization.
- Crucially, Bob does not know which basis Alice used for each photon. If Bob chooses the correct basis, he will accurately measure the bit value. If he chooses the wrong basis, his measurement will be random, effectively scrambling the bit.
- Basis Reconciliation (Public Channel):
- After all photons are sent and measured, Alice and Bob communicate publicly (over a classical channel, like the internet) which basis they used for each photon. They do not reveal the actual bit values yet.
- They then discard all bits where their chosen bases did not match. For the bits where their bases matched, they should theoretically have identical bit values. These matching bits form their raw key.
- Error Correction (Public Channel):
- Due to noise in the channel or Eve's interference, some bits in their raw key might still differ. Alice and Bob use classical error correction techniques (e.g., parity checks) to identify and correct these discrepancies. This process reveals a small amount of information about the key, but it's essential for ensuring they have an identical key.
- Privacy Amplification (Public Channel):
- After error correction, Alice and Bob perform privacy amplification. They use a hash function to condense their key into a shorter, truly secret key. This step removes any partial information Eve might have gained during error correction or from the few photons she successfully intercepted without detection. The result is a final, highly secure shared secret key.
Eve's Dilemma: The Eavesdropping Detection Mechanism
If Eve tries to intercept a photon, she must measure its polarization to gain information. Because she doesn't know Alice's chosen basis, she must guess. If she guesses incorrectly, her measurement will disturb the photon's state. When she then re-transmits the photon to Bob, Bob's subsequent measurement will show a higher error rate than expected. This elevated error rate immediately signals to Alice and Bob that an eavesdropper is present, and they can then abort the key exchange. This inherent detection mechanism is what makes QKD "unconditionally secure."
Other QKD Protocols
While BB84 is the most famous, other protocols exist, such as E91 (Ekert91), which leverages quantum entanglement. In E91, entangled photon pairs are distributed to Alice and Bob. The correlation between their measurements allows them to establish a key and detect eavesdropping. Decoy-state QKD is another variant that enhances security against specific types of attacks.
Key Advantages of Quantum Key Distribution
The unique properties of QKD offer compelling advantages for future data security:
- Unconditional Security: As explained, QKD's security is guaranteed by the laws of physics, not by computational complexity. This makes it impervious to even the most powerful future quantum computers.
- Future-Proofing Data: QKD provides a method to establish keys that are immune to attacks from quantum algorithms like Shor's, securing communications against the "harvest now, decrypt later" threat.
- Eavesdropping Detection: The inherent ability to detect any attempt at interception is a powerful feature that classical cryptography lacks. If an attacker tries to listen, their presence is immediately known.
- Complementary to Post-Quantum Cryptography (PQC): While QKD secures the key exchange, PQC focuses on developing new algorithms that are computationally resistant to quantum attacks. They are not competitors but rather complementary approaches to building a comprehensive quantum-safe security architecture.
Challenges and Limitations of QKD
Despite its profound security benefits, QKD faces practical challenges that limit its widespread deployment today:
- Distance Limitations: Photons are subject to loss and decoherence over long distances. Current fiber-optic QKD systems are typically limited to ranges of 100-200 km without trusted relays (nodes that decrypt and re-encrypt the key, creating potential vulnerabilities). Satellite-based QKD is being explored to overcome this, extending ranges globally.
- Infrastructure Requirements: QKD requires dedicated optical fiber or free-space optical links. It cannot be directly implemented over existing internet protocols without significant infrastructure upgrades.
- Integration with Existing Systems: Integrating QKD into legacy network infrastructure and existing cybersecurity frameworks is complex and costly. It often requires specialized hardware at endpoints.
- Cost and Scalability: The specialized hardware and infrastructure needed for QKD make it expensive to deploy at scale. Research is ongoing to reduce costs and improve the scalability of QKD systems.
- "Man-in-the-Middle" Attacks: While QKD secures the key exchange itself, it doesn't inherently authenticate the parties. A "man-in-the-middle" attack could still trick Alice into exchanging a key with Eve (impersonating Bob) and vice versa. Therefore, QKD must be combined with classical authentication methods to ensure the identities of the communicating parties.
QKD vs. Post-Quantum Cryptography (PQC)
It's crucial to distinguish between Quantum Key Distribution (QKD) and Post-Quantum Cryptography (PQC), as they serve different, yet complementary, roles in the future of quantum security.
- Quantum Key Distribution (QKD):
- Focus: Securely exchanging cryptographic keys using quantum mechanical principles.
- Security Basis: Laws of physics (unconditional security).
- Implementation: Requires specialized quantum hardware (photon sources, detectors, quantum channels).
- Use Case: Point-to-point secure key establishment. Ideal for high-security, high-value data transmission over dedicated links.
- Post-Quantum Cryptography (PQC):
- Focus: Developing new mathematical algorithms that are resistant to attacks from quantum computers, while still running on classical computers.
- Security Basis: Computational hardness of new mathematical problems (e.g., lattice-based, code-based, hash-based cryptography).
- Implementation: Software-based; can be implemented on existing classical computing infrastructure.
- Use Case: Broad application across all digital communications, including web browsing, email, and large-scale data encryption, where quantum hardware is impractical.
Neither QKD nor PQC is a silver bullet. A holistic quantum-safe cybersecurity strategy will likely involve a hybrid approach, using PQC for widespread, general-purpose security, and deploying QKD for ultra-secure, high-priority communications where unconditional security is paramount. Organizations should consider a phased transition strategy, assessing their critical assets and the appropriate blend of these technologies. [Explore advanced cryptography solutions for your business]
Practical Applications and Future of QKD
Despite the challenges, the promise of unconditional security makes QKD an attractive solution for critical applications:
- Secure Government Communications: Governments and defense agencies handle highly classified information that demands the highest level of security, making QKD a vital tool for safeguarding national secrets and strategic communications.
- Financial Transactions and Banking: Protecting sensitive financial data, high-value transactions, and interbank communications from future quantum attacks is paramount for maintaining trust in the global financial system.
- Critical Infrastructure Protection: Energy grids, water supplies, and transportation networks are vulnerable to cyberattacks. QKD can secure the control systems and communication channels that underpin these essential services.
- Healthcare Data Security: Protecting patient records and medical research data from compromise is crucial for privacy and public health.
- The Quantum Internet Vision: QKD is a foundational technology for the development of a future quantum internet, a network where quantum information can be transmitted between quantum computers, enabling new applications like distributed quantum computing and enhanced sensor networks.
Actionable Tips for Organizations Considering QKD
As the quantum threat matures, proactive measures are essential:
- Assess Your Risk Profile: Identify your most sensitive data and critical communication channels that would be most impacted by a quantum attack.
- Monitor Developments: Stay informed about the progress in both quantum computing capabilities and QKD/PQC standardization efforts.
- Pilot Programs: Consider initiating small-scale pilot projects to test QKD solutions in a controlled environment, understanding the integration complexities and operational requirements.
- Hybrid Approaches: Plan for a hybrid encryption strategy, combining classical, PQC, and potentially QKD solutions to provide layered security.
- Vendor Engagement: Engage with cybersecurity vendors and quantum technology providers to understand their roadmaps for quantum-safe solutions.
The journey towards a truly quantum-safe world is complex, but understanding and embracing technologies like quantum key distribution is a critical step in safeguarding our digital future.
Frequently Asked Questions
What is the primary difference between quantum computing and quantum key distribution?
Quantum computing refers to a new paradigm of computation that uses quantum mechanical phenomena like superposition and entanglement to perform calculations. It aims to solve complex problems intractable for classical computers. Quantum Key Distribution (QKD), on the other hand, is a specific application of quantum mechanics for cryptography. It's a method to securely exchange cryptographic keys between two parties, leveraging the laws of physics to detect any eavesdropping attempt. QKD does not perform computations; it ensures the secure establishment of a shared secret key for subsequent classical encryption.
How does QKD detect an eavesdropper?
QKD's security relies on the fundamental principle that measuring a quantum state inevitably disturbs it. When Alice sends photons (encoded with key bits) to Bob, if an eavesdropper (Eve) intercepts these photons to measure their state, her measurement will alter their quantum properties. When these disturbed photons reach Bob, his subsequent measurements will show a higher-than-expected error rate compared to the initial public reconciliation of bases. This elevated error rate acts as an immediate alarm, signaling Eve's presence and prompting Alice and Bob to abort the key exchange.
Is Quantum Key Distribution (QKD) already in widespread use?
While QKD is a proven technology and has been successfully demonstrated in various pilot projects and niche applications, it is not yet in widespread commercial use for general communication. Its deployment is primarily limited by factors such as distance constraints, the need for specialized hardware and dedicated infrastructure (like optical fibers or free-space links), and high implementation costs. However, research and development are rapidly advancing, with satellite-based QKD and integrated photonics promising to overcome some of these limitations, paving the way for broader adoption in high-security environments.

0 Komentar